What Is 1164.68.127.15?
The sequence 1164.68.127.15 appears similar to an IP address, but it is not a valid IPv4 or IPv6 address according to internet networking standards. At first glance, it looks like a standard dotted format used for network identification, but deeper analysis shows structural errors that make it technically invalid.
https://novixanews.co.uk/In normal networking systems, an IP address is used to identify devices on a network so that data can be sent and received correctly. However, 1164.68.127.15 cannot function in this way because it violates the rules of IPv4 addressing, making it more of a malformed or placeholder-style value rather than a real network identity.
This type of string is often searched by users who encounter it in logs, error messages, or suspicious network activity and want to understand whether it is real or harmful.

Why 1164.68.127.15 Is Not a Valid IP Address
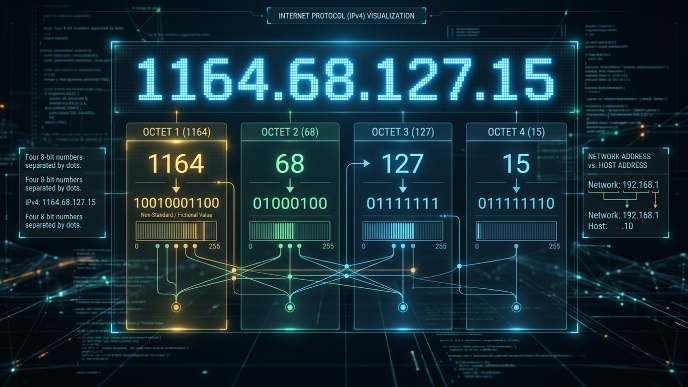
IPv4 addresses follow a strict structure consisting of four numerical segments separated by dots. Each segment, called an octet, must be between 0 and 255. This rule ensures that every possible IP address fits within the 32-bit system used by IPv4.
In the case of 1164.68.127.15, the first segment “1164” exceeds the maximum allowed value of 255. This alone makes the address invalid and unusable in any real network routing environment.
Because of this violation, no router, server, or internet system can assign or recognize this as a functional IP address. It fails validation immediately during network processing.
Where You Might Encounter 1164.68.127.15
Although it is not a real IP address, 1164.68.127.15 may still appear in certain technical environments such as server logs, software debugging outputs, or misconfigured applications.
One common reason is data corruption or formatting errors, where logs incorrectly capture or display values due to system glitches. Another possibility is malfunctioning scripts or bots that generate fake or broken network requests.
It can also appear in security reports or monitoring tools when systems detect unusual or malformed traffic patterns. In such cases, the system flags it as invalid rather than treating it as a real connection.
Technical Breakdown of the Structure
To understand why 1164.68.127.15 stands out, it helps to compare it with proper IP formatting. A valid IPv4 address looks like 192.168.1.1 or 10.0.0.1, where each segment stays within the allowed numeric range.
The first segment in this case, 1164, immediately breaks the rule. Even if the remaining segments (68, 127, 15) are valid individually, the entire structure fails because IP validation depends on all four segments being correct simultaneously.
Networking systems are designed to reject such malformed inputs automatically, ensuring that invalid addresses cannot interfere with routing or communication processes.
Could 1164.68.127.15 Be a Security Threat?
On its own, 1164.68.127.15 is not a functional IP address, which means it cannot directly represent a real attacker or device. However, its appearance in system logs may still be meaningful from a cybersecurity perspective.
Security tools often log invalid or malformed IP entries when detecting suspicious activity such as bot scanning, spoofed requests, or malformed packet injections. These entries can sometimes indicate attempts to probe system vulnerabilities.
In some cases, attackers intentionally send corrupted or fake IP formats to test how systems respond. While 1164.68.127.15 itself is harmless, its presence in logs may warrant further investigation depending on context.
Difference Between Valid and Invalid IP Addresses
A valid IP address must strictly follow numerical boundaries and formatting rules defined by the Internet Protocol standard. Each segment must be a number between 0 and 255, and exactly four segments must be present.
For example, 192.168.0.1 is valid because it meets all conditions. In contrast, 1164.68.127.15 is invalid because it exceeds the allowable range in its first segment.
Invalid IPs like this are often rejected by routers and firewalls instantly, meaning they cannot be used for communication or routing on the internet.
Why Such Values Appear in Logs and Systems
There are several reasons why a value like 1164.68.127.15 might appear in logs even though it is not a real IP address.
One reason is software parsing errors, where systems incorrectly interpret incoming data streams. Another is database corruption or export issues, where formatting breaks during data transfer.
It can also be caused by automated scripts or bots generating malformed requests, either unintentionally or as part of probing activity.
In all these cases, the value is treated as invalid rather than a functional network identity.
How Networks Handle Invalid IPs Like 1164.68.127.15
Modern networking systems are built with strict validation rules to prevent malformed IP addresses from causing issues. When a system detects an invalid format like 1164.68.127.15, it immediately rejects it.
Firewalls and intrusion detection systems often log such entries as warnings or anomalies. This helps administrators identify potential misconfigurations or suspicious activity patterns.
In most cases, invalid IP addresses are simply ignored and do not affect normal network performance or communication.
Should You Be Worried About 1164.68.127.15?
In general, there is no need to worry if you see 1164.68.127.15 in a log or report. It is not a functional IP address and cannot be used to access your system or send data.
However, context matters. If this value appears frequently alongside other suspicious entries, it may indicate a broader issue such as a misconfigured application or automated scanning attempts.
The best approach is to monitor logs for patterns rather than focusing on a single invalid entry.
Final Conclusion on 1164.68.127.15
The sequence 1164.68.127.15 is not a valid IP address and cannot function within any real internet networking system. Its structure violates IPv4 rules because one segment exceeds the allowed numerical range.
While it may appear in logs or technical outputs, it usually indicates an error, malformed data, or system-generated anomaly rather than a real network identity.
Understanding these differences helps users and administrators avoid confusion and better interpret technical logs, ensuring stronger awareness of how internet addressing actually works.